Vulnerability Assessment and Penetration Testing

Why Vulnerability Assessment is essential?
Vulnerability assessment will help an organization in identifying, quantifying, and prioritizing (or ranking) technical vulnerabilities in a system and network, as well has finding the loopholes in their practices and policies. It is an efficient way to assess business risk and improve their security posture.
Why Penetration Testing is essential?
Penetration testing will help an organization in evaluating the security of a computer system or network by simulating an attack from a malicious source, known as a Black Hat Hacker, or Cracker. The process involves an active analysis of the system for any potential vulnerabilities that may result from poor or improper system configuration, known and/or unknown hardware or software flaws, or operational weaknesses in process or technical countermeasures. This analysis is carried out from the position of a potential attacker, and can involve active exploitation of security vulnerabilities. Any security issues that are found will be presented to the system owner together with an assessment of their impact and often with a proposal for mitigation or a technical solution.
- Get detailed analysis of your current exposure to breaches that threaten critical information and assets.
- Identify critical security vulnerabilities and address them.
- Get practical and relevant technical information on how these vulnerabilities can be fixed.
- Assurance to client and business partners that your solution is secure.
- Helps your organization conform to legal and industry regulations.
- Maintan security levels mandated by common standards such as ISO27001, Sarbanes-Oxley, HIPAA and Payment Card Industry Data Security Standard.
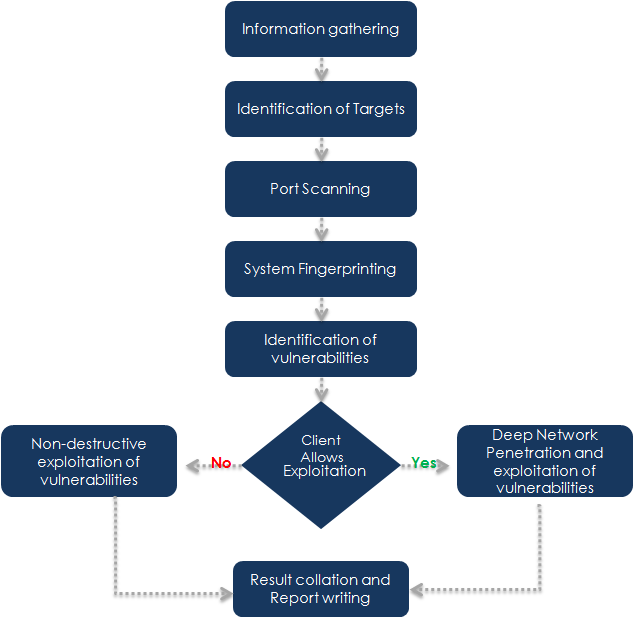
ISECURION uses the following methodology for conducting Vulnerability Assessment and Penetration assessment for your organization:
-
External Penetration Testing is the
traditional approach focused on the servers, infrastructure and
the underlying software comprising the target. It may be
performed with no prior knowledge of the site (black box) or
with full disclosure of the topology and environment (crystal
box).
This type of testing should typically involve a comprehensive analysis of publicly available information about the target and a network enumeration phase where target hosts are identified, analyzed and vulnerabilities within the target hosts or applications should then be verified and the implications assessed.
This assessment helps an organization to evaluate their preparedness against real attacks and significantly reduce IT security costs and provide a better return on IT security investment (ROSI) by identifying and resolving vulnerabilities and weaknesses. These may be known vulnerabilities in the underlying technologies or weaknesses in the design or implementation.
- Internal Security Assessment follows a similar methodology to external testing, but provides a more complete view of the site security. Testing will typically be performed from a number of network access points, representing each logical and physical segment. For an example, this may include tiers and DMZ's within the environment, corporate network or partner company connections.
The phases of our assessment are defined in the flow diagram as below