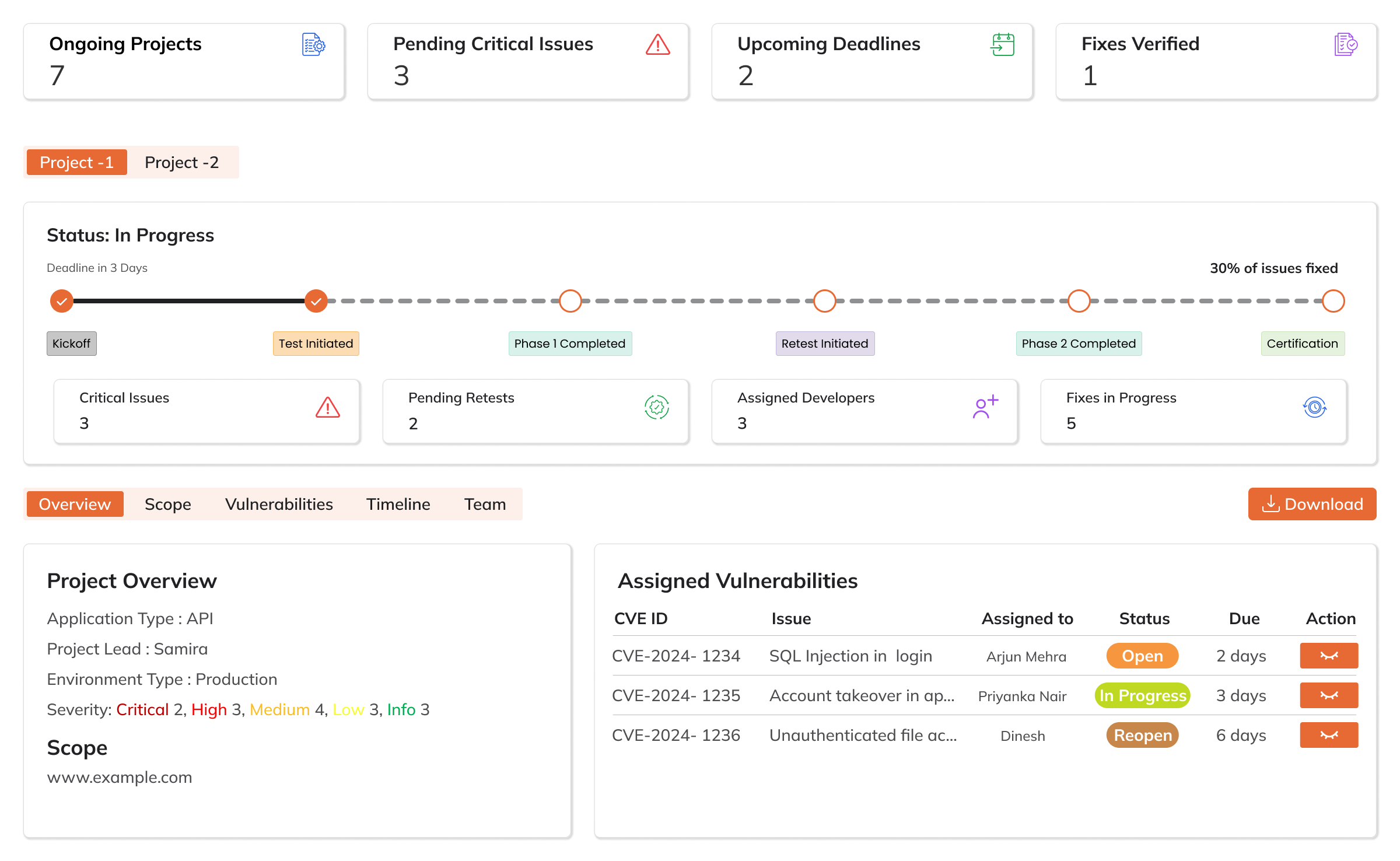
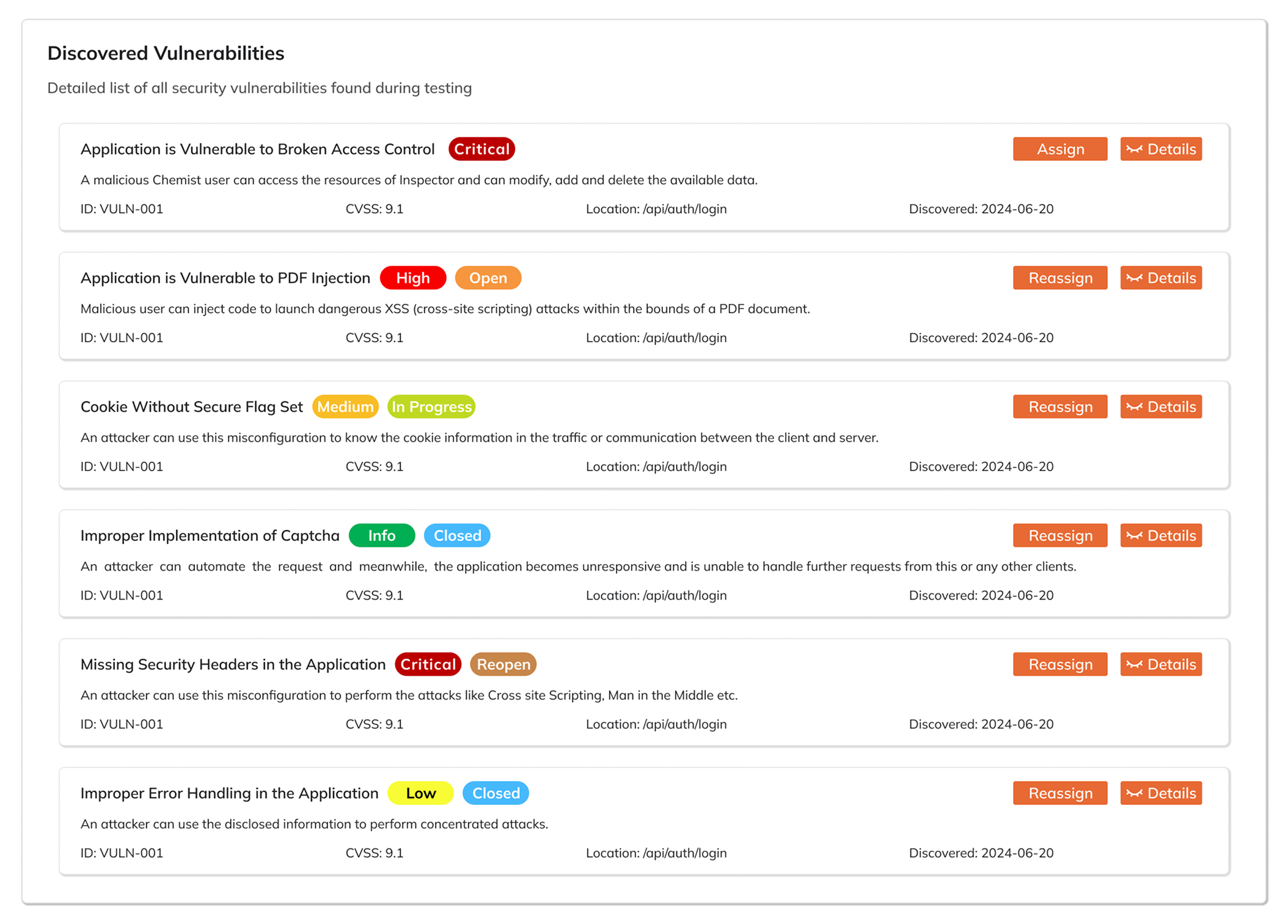
Live Pentest Tracking
Follow every phase of your security assessment in real time. Vulnytics gives you a live window into tester activity - from reconnaissance through exploitation and post-exploitation - so your team is never waiting in the dark. Critical findings surface instantly the moment they're discovered, enabling immediate action rather than a delayed response after a weeks-long engagement cycle.